Search query: hacking
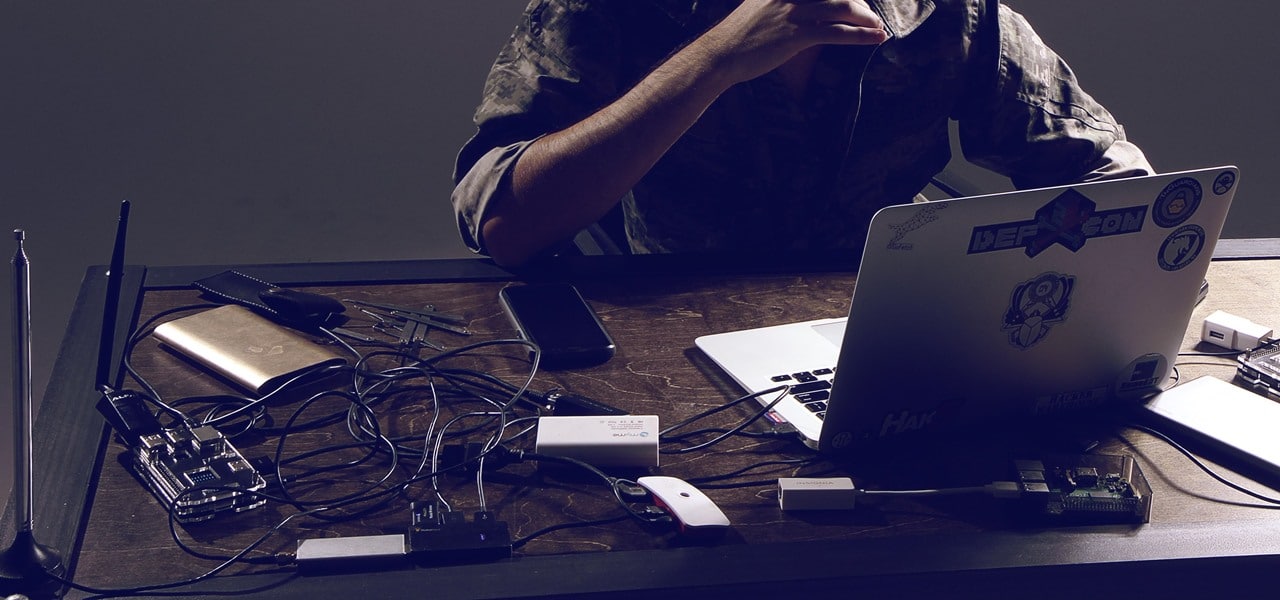
An Unsecured Router Can Tank Your Corporation
The wide publication of attacks on IoT devices and compromised data is enough to make anyone leery of IoT devices in general. Recent attacks like the ...

TITAN NOC With Artificial Intelligence Analysis In Production Operation
(CAMARILLO, CALIF) – Oasis Technology, provider of the leading TITAN anti‐hacking device, announces the new NOC availability of the TITAN data warehou ...

5 Simple But Essential Tips For Startup ICO Developers
ICO developers are true mavericks because they take on gargantuan tasks. Starting an ICO is going to take a lot out of you and it probably already has ...
![Top Security Tips For Online Money Transfers [Infographic] Top Security Tips For Online Money Transfers [Infographic]](https://bitrebels.com/wp-content/uploads/2018/03/safe-money-transfers-online-header-image.jpg)
Top Security Tips For Online Money Transfers [Infographic]
It seems more and more people are worried about their online security. Especially after everything that has transpired in the last few years with secu ...

Your 2018 Business Resolution – Design A Remote Security Protocol
Remote work is the new normal. Whether you’re offering flextime to current employees, have staff working remotely while visiting clients, or hiring ex ...

3 Reasons Managed Video Conferences Make Your Meetings Successful
For a meeting to be considered successful, three things must occur: each person should know what they need to accomplish and by when the agenda needs ...

5 Tips For Better Online Security In A Hostile Business World
You don’t have to be a cybersecurity expert to recognize that there are serious and significant threats all around your business. Expesically your bus ...

Top 4 Cyber Threats All Businesses Face
This last year has been plagued with news about hackers gaining access to email servers, credit information, and even banking data. In fact, in the fi ...

Betting On Cryptocurrencies – The Hottest Topic Of 2018
Cryptocurrencies like Bitcoin are fast, secure, and anonymous online cash - the seemingly perfect currency for online gambling. However, online casino ...

New Symantec Coupons May Be The Answer To The Ever Rising Cyber Crime
Computer hacking has become a big menace in 2017. Did you know that more than 170 million US consumer records stand exposed to this dark web? Given th ...

How A Cloud Access Security Broker Protects Your Business Data
Despite the rapid adoption of cloud applications, some enterprises continue to show hesitance towards migrating to the cloud. Their concern is primari ...

All About Cybercrimes – How You Can Be The Next Prey Of Hackers
We live in a world of cybercrimes, where installing an anti-virus software is simply not enough to protect your data from being stolen and leaked on t ...

Cyber Security Device With Artificial Intelligence Component Hits Milestone
Press Release - Oasis Technology’s TITAN Cyber Security Defense Unit has now completed regional trials with Energy, Finance, and Medical industries an ...

With The Information Age Came The End Of Privacy
What started out as a terror attack on unsuspecting Christmas party goers, which resulted in the deaths of 14 people and 22 injured, ended in a battle ...

6 Important Features Every VPS Server Should Have
The main concept behind a VPS server system is that it is a personalized virtual space that is dedicated to a single user. This space is a part of a m ...