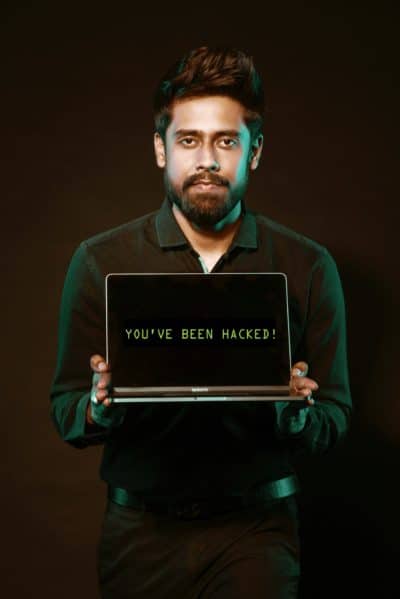
These days, you hear all kinds of horror stories about hackers. Cyber attacks are becoming more and more common – for example, one county in New York State experienced two such attacks in just the first three weeks of 2020. Cyber attacks, hackers, and malware pose a growing threat as geopolitical tensions escalate.
Cyber attacks are growing more sophisticated, too. It’s no longer enough to install an antivirus program on each of your devices – you need a comprehensive security solution that safeguards every device on your network, and protects against social engineering attacks.
But don’t rely on a software solution to protect your data and devices – educate yourself about the basics of cybersecurity, because users represent the weak spot in even the strongest digital armor.
IMAGE: PEXELS
Protect Yourself With A Comprehensive Security Solution
Time was, you could just install an antivirus program on your home computer and consider yourself protected from viruses and other malware. But those days are gone. You might not even have a laptop or desktop at home anymore – about 20 percent of Americans today go online primarily using a mobile device, such as a smartphone.
The rapid advance of digital technology has also placed more devices than ever in the average home. A third of American households contain three or more smartphones, and many homes also include other devices, like laptops or desktops, tablets, smart home devices, and smart appliances.
If you’re putting separate antivirus programs on all of your smartphones, tablets, and computers, you’re leaving yourself at risk. A comprehensive solution for virus and malware detection and removal covers all of your devices with the same software.
It goes beyond malware protection to offer extra security for online banking and shopping, child safety settings, fraud, and phishing scam alert ransomware removal, password management, and privacy shields.
Arm Yourself With Cyber Security Know-How
Cybersecurity experts agree that, no matter how comprehensive or beefy a software solution is, human users can always find a way to undermine it. That’s because cybercrime pays, and criminals desperate for a buck have discovered that you don’t need a lot of specialized computer training to succeed as a hacker.
Instead, they’ve realized that social engineering attacks are often just as effective at getting them into your network, where they can access your valuable personal information, including passwords, security question responses, and financial data.
Social engineering attacks exploit vulnerabilities in human psychology, rather than weaknesses in computer software. A typical example is an old scam in which someone contacts you via email or Facebook Messenger, claiming to be a relative in trouble – the scammer hopes you’ll panic and wire them money before you stop to think about verifying the story.
Phishing scams, which use email, social media, and instant messaging services, are the most common form of social engineering. Hackers also hope to take advantage of users who don’t understand the basics of network security. For example, did you know that most manufacturers of routers and wireless gateways set up all of their devices with the same admin credentials?
These are different from the SSID and password you use to access your home wifi network; they give you control over the router itself and the network configuration, and hackers can typically find these credentials published online, free for the taking.
That means that if you haven’t changed your router’s admin credentials, your network is vulnerable, and you could find yourself the victim of a hacker like the one who accessed a family’s Ring security camera to harass their little girl in her own bedroom – or worse.
Once on your network, hackers could lock you out of it, and exploit inherent vulnerabilities in your smart devices’ software to take control of it. They could even gain access to your smartphone, tablets, laptops, and other devices that contain sensitive personal data.
Keep hackers off your home network. Learn how to lock down your router and secure your home network. A skilled or determined hacker might still get through your defenses, but you’d at least be deterring the vast majority, who are looking for an opportunity to make some easy money.
It’s the same theory as locking your doors and windows – sure, someone who really wanted to could still get in. Still, basic security measures deter the opportunistic thieves, who will look elsewhere for easier pickings.
When it comes to protecting your personal data, you can’t be too safe. You need to keep your sensitive information private, and you need a multi-pronged approach to do so successfully. With a comprehensive cybersecurity solution and some basic knowledge of cybersecurity, you can protect yourself from cyber attacks and continue to enjoy the perks of technology.
If you are interested in even more technology-related articles and information from us here at Bit Rebels, then we have a lot to choose from.

COMMENTS