Search query: cyber security
Under Attack? – Digital Forensics Drives Cybersecurity Inquiries
Cybersecurity is a pressing issue for all businesses today, and hackers and their kin become sneakier all the time. Take, for example, the leap from b ...
Tips For Succeeding In A Career In Cybersecurity
Are you considering a career in cybersecurity? This is one of the best career paths to follow moving forward; it is an industry that will be in great ...
The Biggest Cybersecurity Threats
While much of the world has focused on the spread of the COVID-19 pandemic, the tech community has been stepping up to provide assistance. At the same ...
How Are Tech Experts Protecting Themselves Against Cybersecurity Threats?
Cybersecurity continues to be a big threat to the smooth operation of businesses, including those operating in the tech sphere. The Annual Data Breach ...
Why Do Businesses Need To Level Up Their Cybersecurity?
In today’s modern world, almost every business entity leverages digital technology for a variety of purposes that can include production, distribution ...
Thierry LeVasseur, Vancouver Internet Security Expert Describes Four Types Of Cyber Attackers
One of the most debilitating occurrences that can happen to you or your business is discovering that your computer has become the victim of a cyber at ...
Everything You Need To Know About Creating A Cybersecurity Plan To Protect Your Small Business
Does your small business have a cybersecurity plan? Here’s how to create one that will protect your business from cyber risks and threats large and sm ...
Automated Lifecycle Management Improves Cybersecurity Protections
Understanding the principles of automated lifecycle management and employing them to create a cyber secure data system should be a priority for your b ...
Boosting Cybersecurity With AI – How Is It Done?
With businesses, companies as well as government facilities moving entirely online, security breaches have become one of the biggest disasters a compa ...
5 Ways 3D Printing Is Susceptible To Cybersecurity Risks (And How To Mitigate Against Them)
3D
printing (also known as additive manufacturing) is making inroads into various
fields including agricultural (such as tractor parts),
industrial, ...
![Why Cybersecurity Training Is Crucial For Your Business [Infographic] Why Cybersecurity Training Is Crucial For Your Business [Infographic]](https://bitrebels.com/wp-content/uploads/2018/07/cyber-security-training-header-image.jpg)
Why Cybersecurity Training Is Crucial For Your Business [Infographic]
Whilst it might go against the common perception, the greatest threats to your business are not external – they are internal. Now don’t panic, I’m not ...
7 Reasons We Need A Serious Overhaul In Healthcare Cybersecurity
Cybersecurity in the healthcare industry has been a passing concern for hospital administrators and other high-ranking positions for years, but the ne ...

Why Cybersecurity Training Should Never Be Overlooked
Cybersecurity is the process of identifying, responding, and stopping security breaches and other cyber incidents. Though cybercrimes can be both mino ...
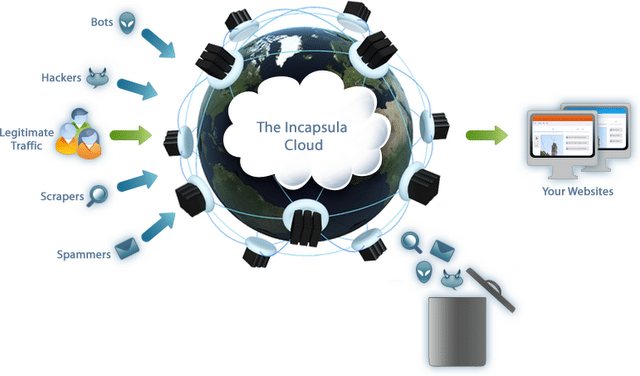
Incapsula: Website Security Protection To Keep Cyber Cyclopee Out
Recently, I wrote a bit of a rant about the ins and outs of protecting your website from Zombie hackers, malicious code snakes and spammers in Keep Bl ...
![Obama vs. Romney On Cybersecurity [Infographic] Obama vs. Romney On Cybersecurity [Infographic]](https://bitrebels.com/wp-content/uploads/2012/10/cybersecurity-obama-vs-romney-infographic.png)
Obama vs. Romney On Cybersecurity [Infographic]
There is no doubt the American Presidential election has garnered a lot of "scandals" and news worthy events for each candidate to express and correct ...