Not a single Internet user doesn’t know that a certain evil is at large on the Internet. They are called hackers and sometimes cause havoc to secure systems online. What most people don’t know is that hackers are mostly just voyeurs. They break into systems to get access to things they are interested in even though the data is not for their eyes to see. They rarely cause any damage to any files or data that they may come across. Presented below are the most prominent hacker profiles on the hacking scene.
When you read about companies getting hacked and the amount of damage they have caused, usually written in dollars, it’s a little misleading. What the report usually means is not files that have been deleted but the amount it will cost to replace systems and patch the security holes used to break in.
Profiling a hacker is quite easy, catching him/her is a whole different story. The easiest ones to catch are the ones that commit the hack and then brags about it. There is always a trace, you just have to find it. The hacks that are the most dangerous are the ones that we never hear or know about. They are the kind of hacks that go unnoticed and keep being active in systems used by million of people.
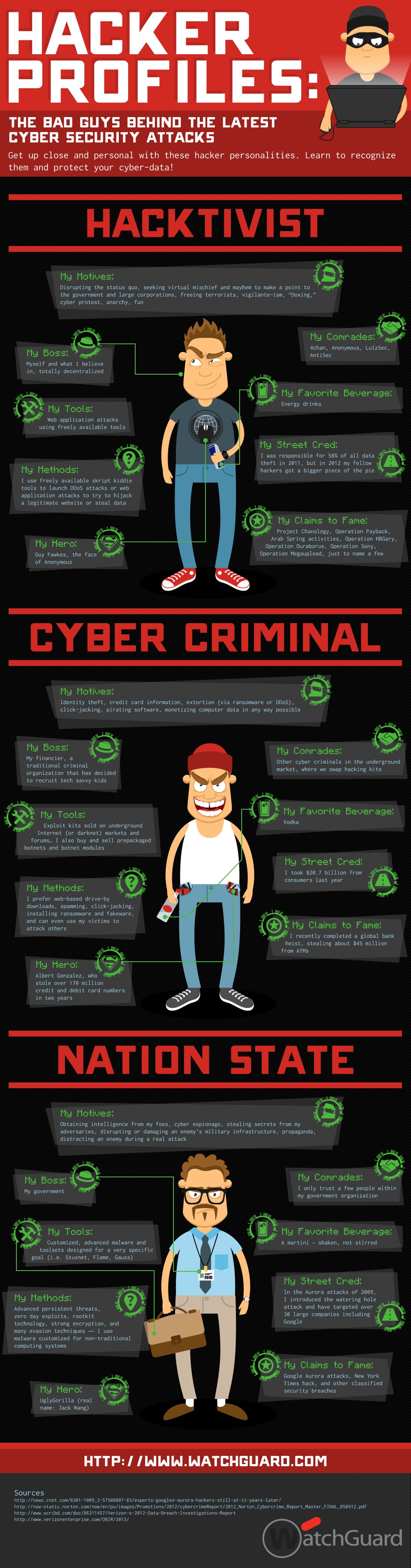
This infographic called “Hacker Profiles: The Bad Guys Behind The Latest Cyber Security Hacks” (created by WatchGuard) is a brief look at the most prominent hackers out there today. The infographic outlines a number of things about each hacker type and what drive them.
If you have ever experienced identity theft or had your data stolen or deleted, you know how frustrating it can be to put everything back in order. The Internet is not an insecure place to be, you just have to implement the necessary means of security. These hacker profiles should give you a hint about what you can do to keep them from getting access to your data. The one common trait all hackers showcase is that they do it because they can and because they want to show how smart they are.
COMMENTS